How to install a certificate using the ACME protocol?
This guide describes a complete and reliable procedure to install a Trustsign, Sectigo or Comodo SSL certificate using the ACME client acme.sh.
It includes common production errors and their associated solutions.
0. DNS preparation
Before any installation, make sure your domain points to your server.
Type: A
Name: @
Value: Server IP
Without this configuration, certificate generation will fail.
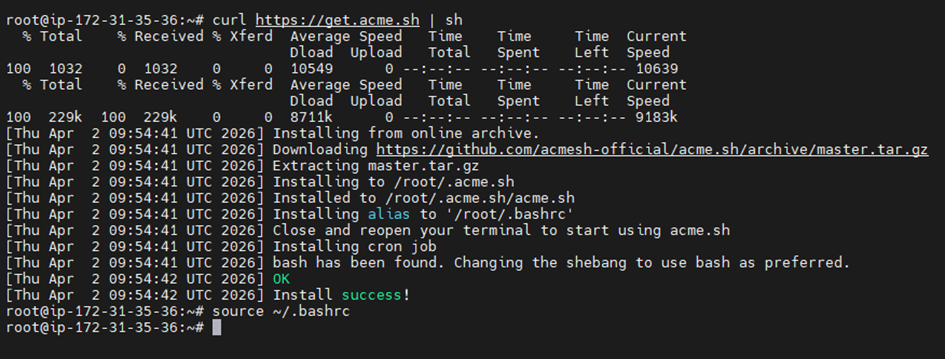
1. Installing acme.sh
Install the ACME client on the server.
curl https://get.acme.sh | sh && source ~/.bashrc
Possible errors:
- curl command blocked → check internet connection
- acme.sh not available → reinstall as root (use: sudo su)
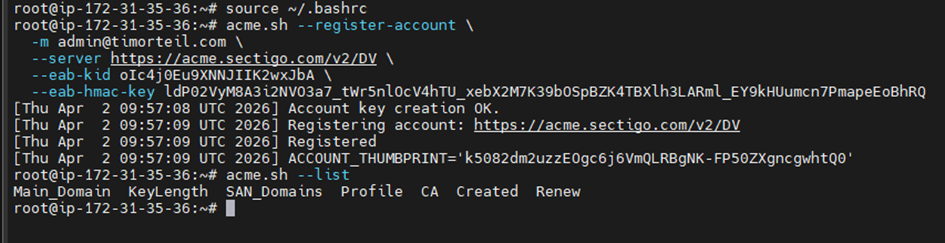
2. ACME account registration
Register the account using the EAB credentials provided when purchasing your certificate:
acme.sh --register-account
-m admin@yourdomain.tld
--server <URL provided in your HTTPCS dashboard>
--eab-kid YOUR_KID
--eab-hmac-key YOUR_HMAC
Possible errors:
- curl command blocked → check internet connection
- acme.sh not available → reinstall as root (use: sudo su)
3. Certificate generation
Create the certificate using HTTP validation (webroot):
acme.sh --issue
-d yourdomain.tld
-w /var/www/html
--server <URL provided in your HTTPCS dashboard>
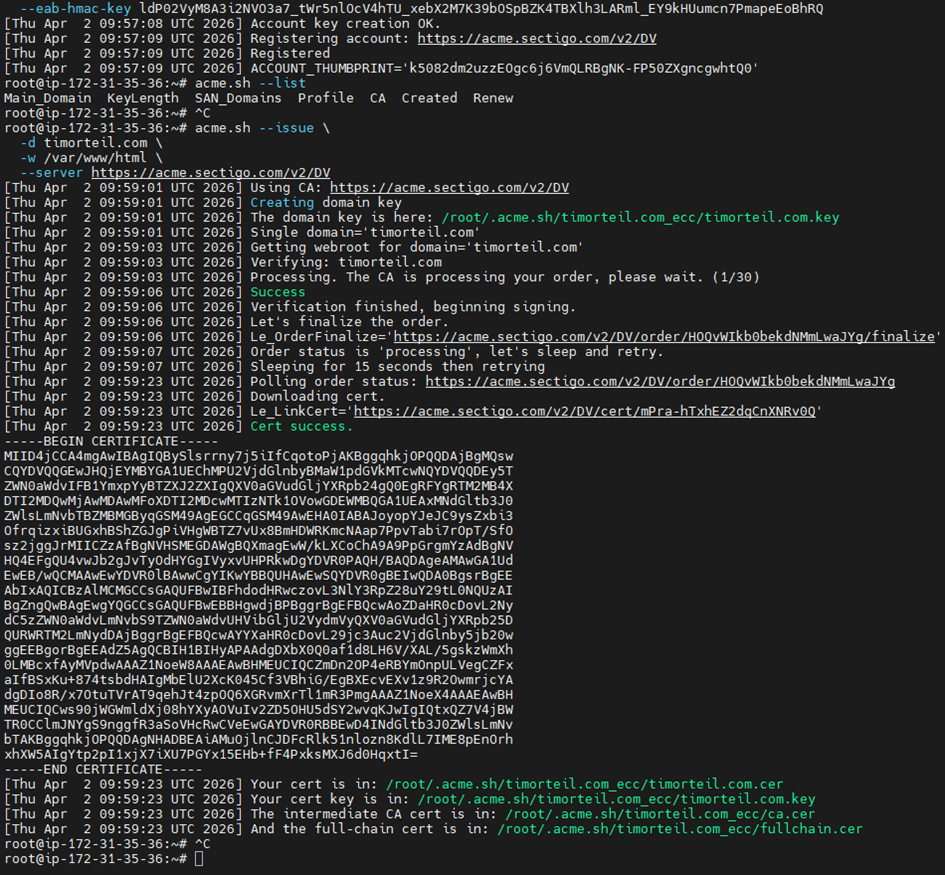
Possible errors:
- Port 80 closed → open firewall
- Wrong webroot → check in /var/www/*
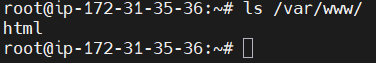
* : To find your web root directory, you can use the command ls /var/www/.
In this tutorial, the directory is named html, but this may vary.
4. Certificate installation and system deployment
Install the certificate into the system /etc/ssl and reload Nginx.
acme.sh --install-cert -d yourdomain.tld
--key-file /etc/ssl/private/yourdomain-acme.key
--fullchain-file /etc/ssl/certs/yourdomain-acme.crt
--reloadcmd "systemctl reload nginx"
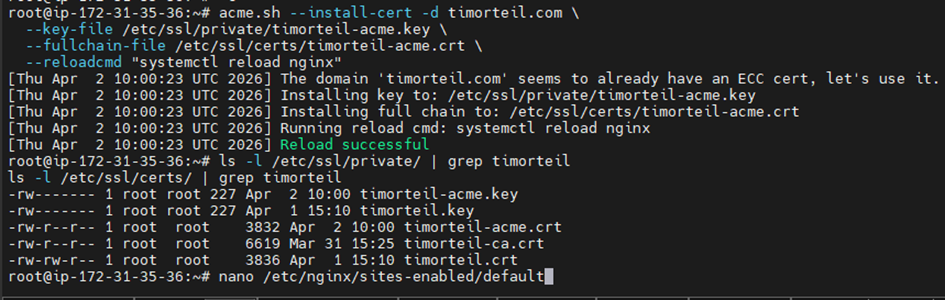
ls -l /etc/ssl/private/<br> ls -l /etc/ssl/certs/
Possible errors:
- Permission denied → run as root
- Wrong path → verify SSL paths
5. Nginx configuration
Configure Nginx to use the ACME certificate.
ssl_certificate /etc/ssl/certs/yourdomain-acme.crt;
ssl_certificate_key /etc/ssl/private/yourdomain-acme.key;
ssl_trusted_certificate /etc/ssl/certs/yourdomain-ca.crt;
systemctl reload nginx
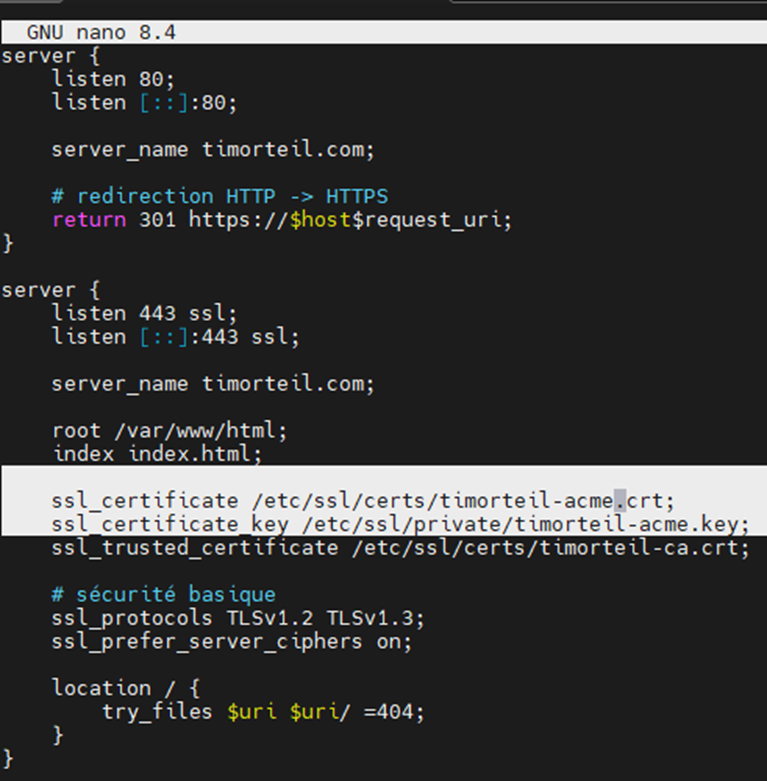
Possible errors:
- Wrong file loaded → check sites-enabled
- Forgot to reload nginx → systemctl reload nginx
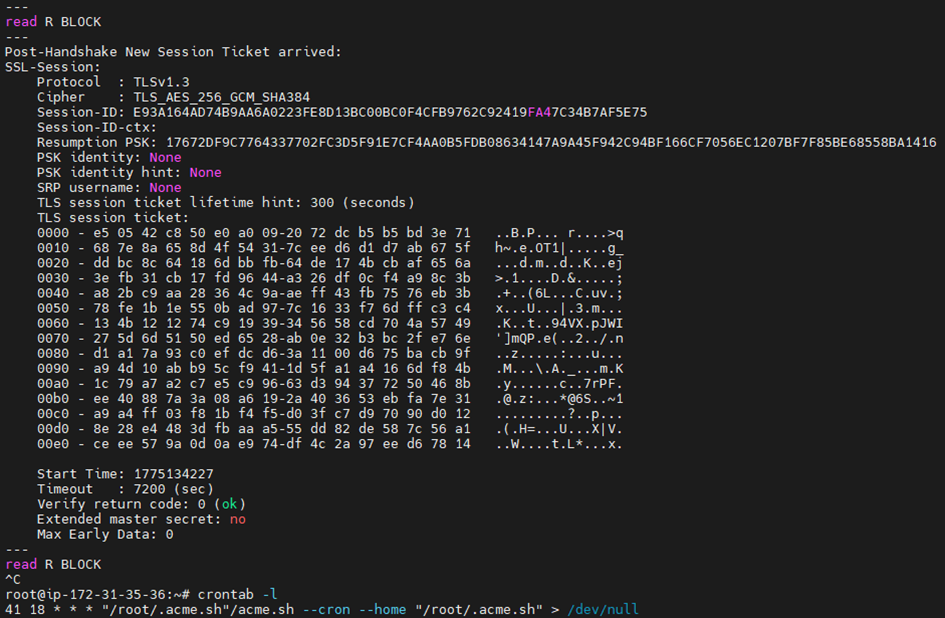
6. SSL verification
Verify using openssl and browser.
openssl s_client –connect yourdomain.tld :443 – servername yourdomain.tld
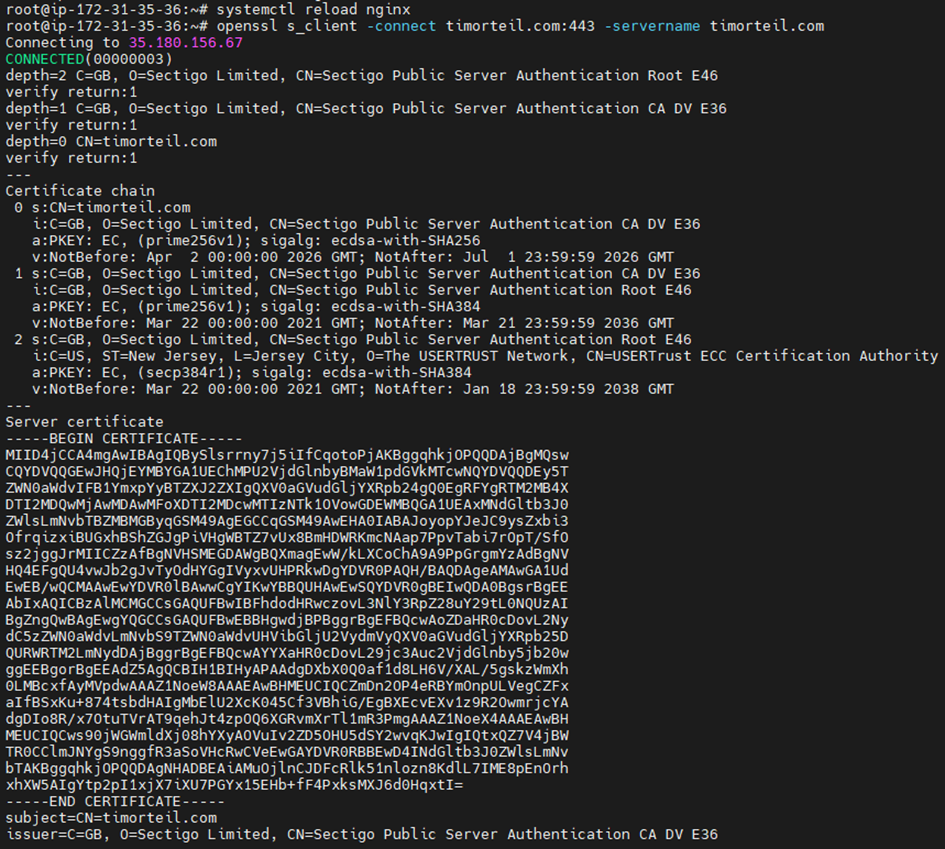
Possible errors:
- Old certificate displayed → clear browser cache
- Wrong certificate → check nginx paths
7. Browser verification
Confirm that the certificate is valid on the client side.
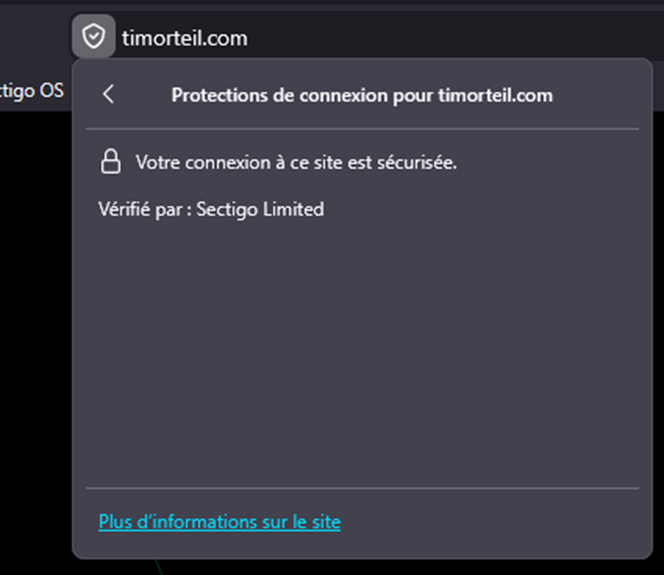
Possible errors:
- Certificate not secure → CA chain issue
8. Automatic renewal
Check that the cron job for automatic renewal is present.
crontab -l
Possible errors:
- No cron job → reinstall acme.sh
Critical points to check before installation
- The domain points to the server (DNS configured)
- Port 80 is publicly accessible
- Nginx is running
- SSL paths are consistent
Best practices
- Always test with openssl after installation
- Never remove old certificates without verification
- Check the cron job regularly
Conclusion
The installation is complete when the certificate is active, recognized by the browser, and automatically renewed.