Cyber Security solution guaranteed zero false positive


Zero false positive guaranteed vulnerability scanner
Multiple solutions exist to secure a website or a web application: this has logically led to a significant increase in the number of alerts for IT teams to manage.
How exploitable and dangerous is a detected vulnerability? Hunting down false positives constitutes a considerable waste of human resources which can have a significant impact on your business.
That's the reason why HTTPCS has developed a web vulnerability scanner guaranteed zero false positive.
False positive: the false alarm that wastes time and money
Definition of a false positiveAccording to Wikipedia, « A false positive error, or in short a false positive, commonly called a "false alarm", is a result that indicates a given condition exists, when it does not.»
The false positive applied to a cybersecurity product is therefore:
- In the case of an anti-malware, anti-spam, or IDS (Intrusion Detection System): a healthy object (cookie, file, website,...) is declared infected i.e. considered dangerous by the tool, whereas it is not. This false detection will then send an alert, which has no reason to be!
- In the case of a vulnerability scanner: a so-called 'security flaw' that is not a security flaw. A vulnerability detected by the tool which is in no case exploitable by a hacker and which therefore does not involve any danger for the security of the website or the web application.

Types of false positives
There are several types of false positives related to cyber securityFalse positive by signature
This false detection can occur when a cyber security tool detects, within a non-malicious object, a signature identical to that of a known unhealthy object. For example, a web vulnerability scanner could identify a software plugin version as potentially vulnerable if its version is close to a version flagged as vulnerable. Its signature will look similar, so the scanner might report a false positive.
False positive by behaviour
Most cyber security solutions have multiple levels of protection and incorporate multiple technologies of parasite detection. One of these methods is to make a suspicious object act and observe its behaviour. A vulnerability scan could be misled by a configuration file (simply written on the front end) which is in no way a flaw.
Dishonest False Positive
The dishonest false positive is an attempt by some to report a number of fictitious infections on a system. Indeed people try to sow doubt by developing many trapped websites. Browsing randomly, the security tool will detect many false positives to induce the user to buy some detection software.

Impacts
What is the impact of these false positives on cyber security?The massive amount of time lost in managing and analysing false positives (i.e. false alarms) results in time lost dealing with "real" alarms. Indeed, both software and human resources will be called upon for an alert that shouldn't be raised.
When a tool generates many false positives, in addition to wasting time, confidence in that tool is impaired. False positives are costly errors due to reduced productivity.
Web Vulnerability Scanner guaranteed zero false positive
Vulnerability scanning makes it possible to detect security flaws on a website or a web/application and system perimeter:Web Security
Detecting security flaws on a website
Application Security
Rising vulnerabilities of a web application
System security
Scan of security flaws in a system (web server)
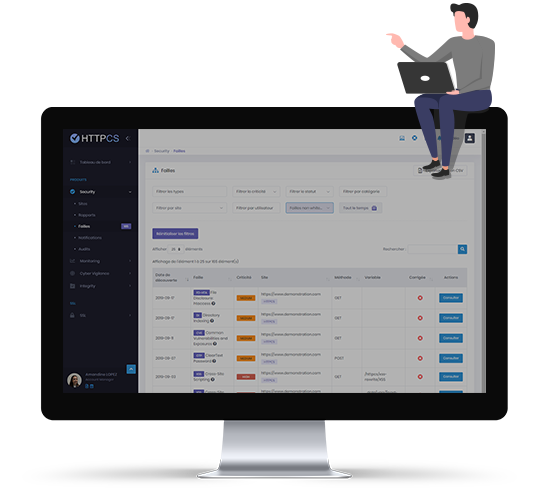
HTTPCS Security scanner ensures zero false positive vulnerability reports
We guarantee our solution will only identify vulnerabilities that can be exploited by hackers.
How can HTTPCS guarantee zero false positive?
The HTTPCS vulnerability scanner details each vulnerability through a report. This presents the flaw, the risks involved, its criticality level and the corrective measures to be applied.
As proof of the zero false positive guarantee, our solution allows you to replay the attack in one click to simulate what a hacker might have done in real life.
Frequently asked questions about false positives in IT
What is a false positive in IT?
A false positive is a false detection, a false alarm. In the case of a vulnerability scanner, it is the fact of detecting vulnerabilities that are not vulnerabilities because they are not exploitable.
How to recognize a false positive?
In cybersecurity, to recognize a false positive, it is enough to simulate an attack and see if the detected flaw is really exploitable. If not, it's a false positive.
False positive and false negative in web security
A false positive is a false alarm (false positive test) while a false negative is the absence of an alarm when there is an exploitable flaw (false negative test).
How do we make sure it's not a false positive?
In order to verify that a vulnerability is not a false positive (=an unexploitable vulnerability), in the case of the HTTPCS vulnerability scanner, click on the "simulate attack" button to have proof that the vulnerability is exploitable.